CVE Watchlist
Notification of new vulnerabilities in monitored products.
Benefits of the CVE watchlist
- Monitoring deployed products for new vulnerabilities.
- Direct assignment to teams, in-house products and self-hosted services.
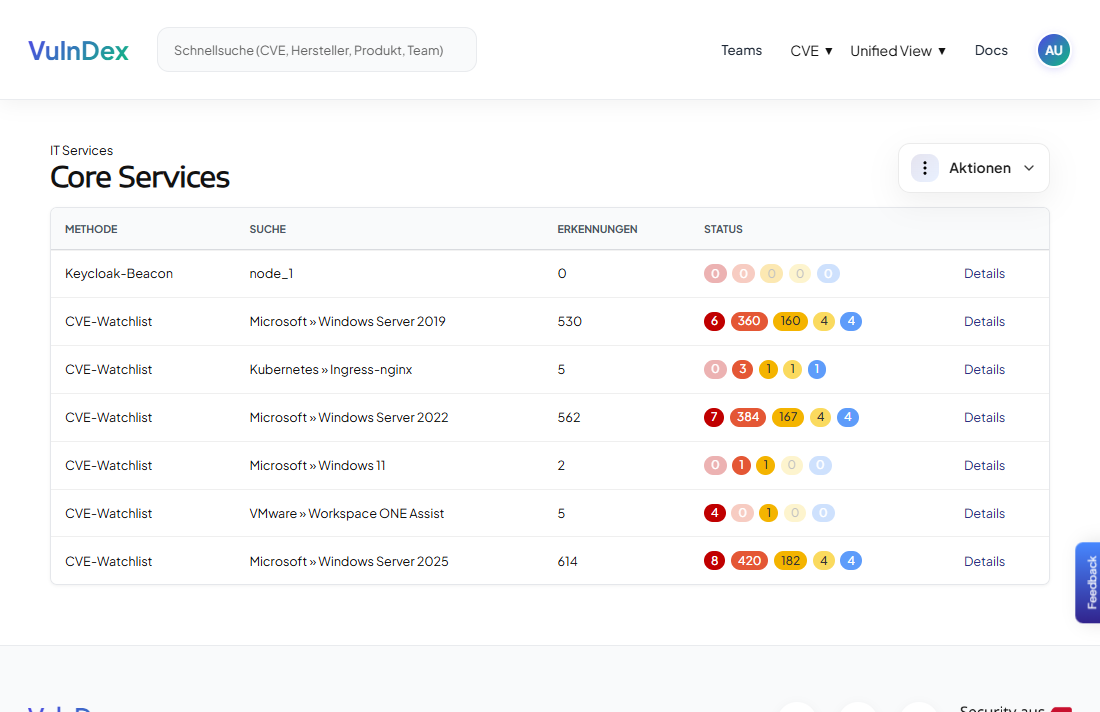
- Overview of the current status of individual CVEs within the team.
Overview of vulnerabilities in software in use
The CVE watchlist links public vulnerability information to your products, versions and teams. Relevant CVEs are automatically assigned and enhanced with additional information from the Vulnerability intelligence. This enables teams to identify at an early stage which vulnerabilities affect the software they use.
Direct assignmentAssign product
Published vulnerability information is directly linked to the monitored software, and the team is notified.
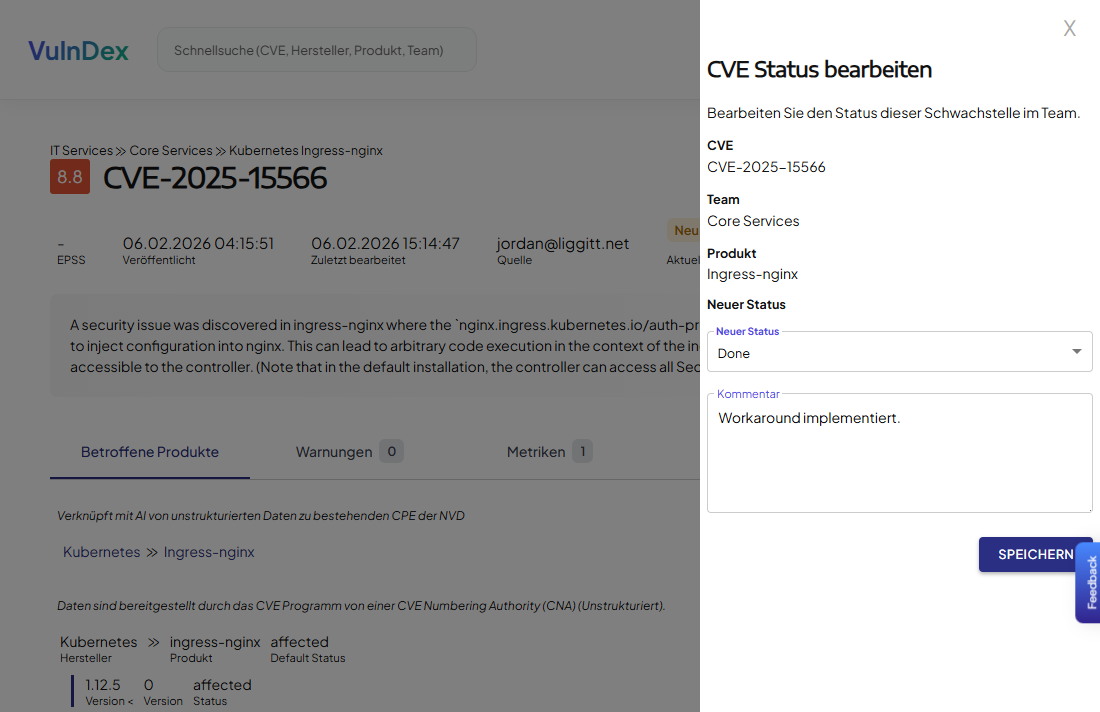
Status managementUser management
The integrated status management system allows the security team to see whether a new detection has already been dealt with.
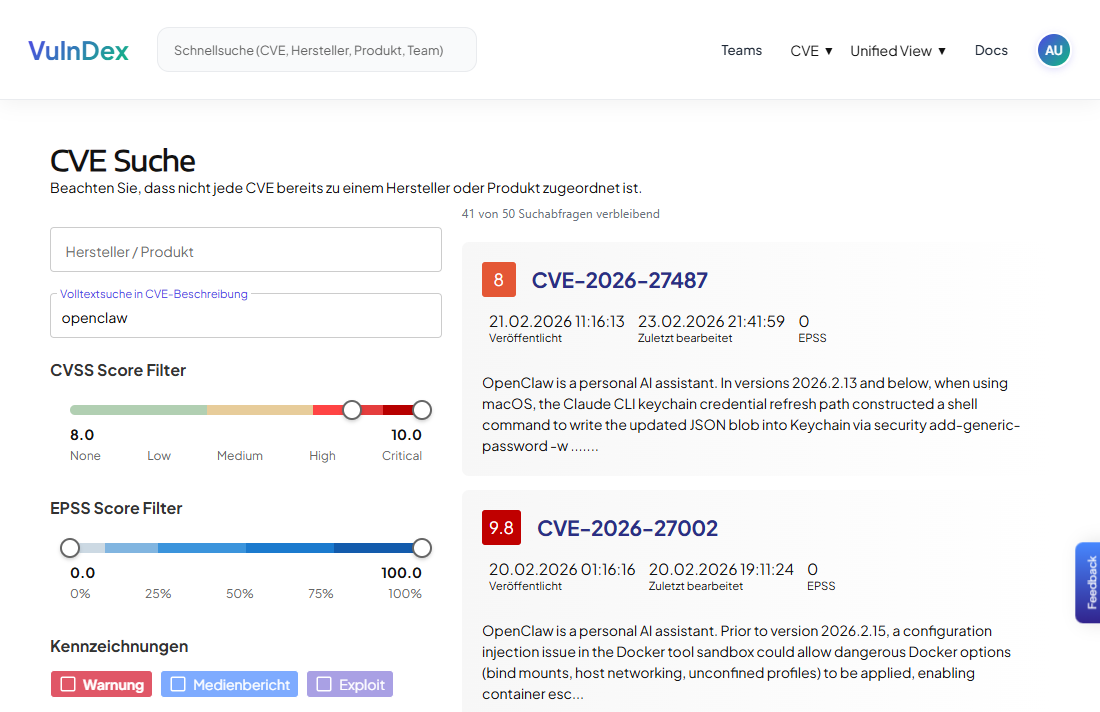
Prioritisation through vulnerability intelligence
CVE entries are enhanced with additional information such as details on exploits or recent mentions in media reports or on social media.
Self-organised monitoring
Teams can maintain their own watchlists and keep track of relevant CVEs. The security team is provided with a central overview of the software in use.
Let’s achieve more together!
Link public CVE information to the software you use and track the processing status in a shared database.
Security made in Austria
- Sovereign cloud architecture
Operated on servers in Austria in collaboration with European partners - Privacy according to European standards
Responsible handling of personal data - Certified cyber security from Austria
Certification in accordance with the Cyber Trust Austria® Standard Label
Request a demo
Sehen Sie, wie VulnDex Sie im Umgang mit Schwachstellen unterstützt.